OpenVPN + DD-WRT: CCD files not restricting users VLAN access while OSPF is enabled.
Here's the scenario. I've set up my OpenVPN on my DD-WRT Asus router. My OpenVPN network is 10.1.1.0 / 255.255.255.0 ( tun2 ). I can connect to my VPN Server remotely by tethering my laptop to my mobile phone ( On my Wireless Provider's Network ) then connecting over to my external ISP IP on which my OpenVPN server is residing on. I see the CCD files get applied to my User, as they should, restricting me to a specific VLAN ( 10.30.0.X ). My CCD config is:
CCD File:
push "route 10.30.0.0 255.255.255.0"
Now the router where my OpenVPN resides also has a local IP address from the local subnet that is my local network and an external one for my ISP. This local VLAN IP is on br0: 192.168.0.100 . My external ISP IP is on vlan2@eth0 : 123.123.123.100 .
Connecting to devices on 10.30.0.X, works fine, which is expected. But I can also connect to devices on my local network which is on 192.168.0.X . I should not be able too. When I check where I logged in from on the target machine, the IP listed is 192.168.0.100, which is the OpenVPN Server local IP, NOT my VPN IP 10.1.1.2 . Because of this, restricting traffic via F/W rules doesn't work against 10.1.1.0/24 .
Appears when I initiate an SSH connection from my laptop to a local machine on 192.168.0.X, for example, the OpenVPN server forwards those packets from tun2 over to br0 from which it then initiates a connection to the target machine. Since the connection appears to be routed through br0, which is on 192.168.0.100, the connection to other machines on the local subnet of course works.
This Asus router is also running OSPF. ( This is a routing protocol that establishes routes automatically. )
Including a visual of the setup.
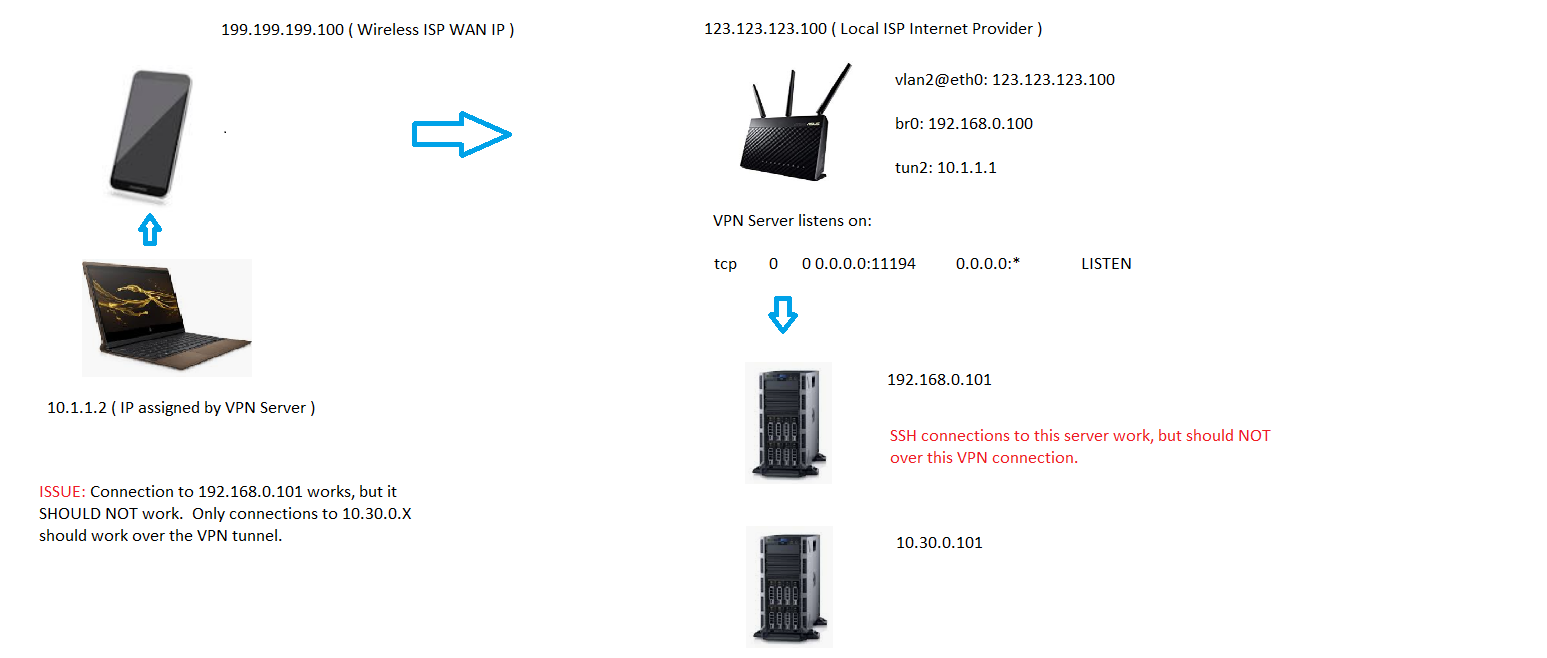
Notice above that traffic to the 10.30.0.101 IP works as it should. The configuration for the whole setup is as follows:
OpenVPN Server Settings:
dh /jffs/etc/openvpn/dh.pem
ca /jffs/etc/openvpn/ca.crt
cert /jffs/etc/openvpn/cert.pem
key /jffs/etc/openvpn/key.pem
tls-auth /jffs/etc/openvpn/ta.key 0
keepalive 10 120
verb 3
mute 3
syslog
writepid /var/run/openvpnd.pid
management 127.0.0.1 14
management-log-cache 100
topology subnet
script-security 2
port 11194
proto tcp4-server
cipher aes-256-cbc
auth sha256
client-connect /tmp/openvpn/clcon.sh
client-disconnect /tmp/openvpn/cldiscon.sh
client-config-dir /jffs/etc/openvpn/ccd
comp-lzo adaptive
tls-server
ifconfig-pool-persist /tmp/openvpn/ip-pool 86400
client-to-client
push "redirect-gateway def1"
tls-cipher TLS-DHE-RSA-WITH-AES-256-CBC-SHA256
tcp-nodelay
tun-mtu 1500
mtu-disc yes
server 10.1.1.0 255.255.255.0
dev tun2
auth-nocache
OpenVPN Client Configuration:
client
dev tun2
proto tcp
remote my.website.com 11194
resolv-retry infinite
nobind
persist-key
persist-tun
ca ca.crt
cert GuestUser.crt
key GuestUser.key
remote-cert-tls server
tls-auth ta.key 1
cipher AES-256-CBC
auth SHA256
comp-lzo
verb 3
auth-nocache
F/W Rules:
# ----------------------
# VPN Specific
# ----------------------
# Allow external connections to 11194
iptables -A INPUT -p tcp --dport 11194 -d $(nvram get wan_ipaddr) -j ACCEPT
iptables -A INPUT -p udp --dport 11194 -d $(nvram get wan_ipaddr) -j ACCEPT
# Allow Web Traffic
iptables -t nat -A POSTROUTING -s 10.1.1.0/24 -j MASQUERADE
# Block VPN clients from accessing anything else on the local network.
iptables -A INPUT -s 10.1.1.0/24 -j REJECT --reject-with icmp-port-unreachable
iptables -A OUTPUT -s 10.1.1.0/24 -j REJECT --reject-with icmp-port-unreachable
Client CCD File:
push "route 10.3.0.0 255.255.255.0"
The Resolution
The resolution to this was much simpler then it appeared at first. Turns out this line:
push "redirect-gateway def1"
was causing all traffic to pass through the default gateway, which in this case is 192.168.0.100. So the CCD files were effectively ignored. Removed the above line from the configuration and VLAN restriction based on CCD definition worked like a charm.
HTH,
TK
REF: https://community.openvpn.net/openvpn/wiki/RoutedLans
REF ( Own Post – OpenVPN ): https://forums.openvpn.net/viewtopic.php?f=4&t=29447
REF ( Own Post – DD-WRT ): https://forum.dd-wrt.com/phpBB2/viewtopic.php?p=1187018#1187018


