Setting up RT-AC5300 ASUS firmware with serial cable on Ubuntu.
- Open the back of the router by removing the 4 screws hidden underneath the rubber stands.
- Remove both covers and carefully place the router motherboard on your desk.
- Make sure the boards Ethernet ports are facing the left and the Serial pins positioned on the right but in the bottom right corner.
4. Connect your serial cable to your computer and the connectors to the corresponding pins as shown below. DO NOT plug in the VC power cable (red) this can fry the router. This is what your serial cable should look like:
5. Install screen (Ubuntu). This will allow you to see what the router is doing through the serial cable. See more at step 11.
- sudo apt install screen
6. Install TFTP (Ubuntu)
- sudo apt install tftp-hpa
7. Connect your Ethernet cable to your computer from the router board. We must open a connection between your computer and the router.
8. Set up a static IP on your wired network. (Ubuntu)
- Go to your settings
- Select “network”
- Select IPV4
- Change your IPV4 from DHCP to manuel
- Address: 192.168.1.X choose any available IP on this network.
- Netmask: 255.255.255.0
- Gateway: 192.168.1.1
9. Put the router board into recovery mode using the following steps.
- Turn off the router. Remove the power cord, or just press the power button.
- Remove the Ethernet cable temporarily from the board.
- Press and hold the reset button on the bottom left.
- Press and hold the reset button for 30 seconds.
- After 30 seconds, plug the power cable back in. DO NOT release the reset button.
- Hold the rest button for another 30 seconds until the power light flashes slowly or the console returns a message.
10. Download the proper .trx firmware file for the RT-AC5300 from ASUS.
– https://www.asus.com/au/supportonly/rt-ac5300/helpdesk_download/
– Select BIOS and FIRMWARE
– Download the latest FIRMWARE for the RT-AC5300 and keep it on your desktop. You will have to extract the zip file (If you get one) to access the .trx binary file.
11. Open a second tab on your terminal and prepare to monitor your flash using screen.
type in your command line: screen /dev/ttyUSB0 115200
12. Use TFTP to flash the .trx file to the router. You can monitor your progress through the serial cable using screen.
- Type the following commands in order:
-
- tftp 192.168.1.1
tftp> binary
tftp> trace (Tracks the packets being sent)
tftp> put filename.trx
tftp> quit
- tftp 192.168.1.1
- Wait for the flash to complete. This usually takes about 5-10 minutes.
13. Change your wired network back to DHCP now that the router has its own unique IP.
14. Visit your WiFi internet link.
15. Create A password for the new network and the router. After this is completed re login to your router UI make sure to edit your internet link accordingly.
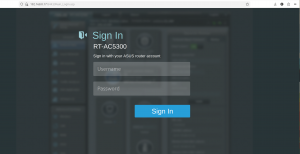
16. Log in to your router UI ex https or http://192.168.0.X and login using you router name and password:
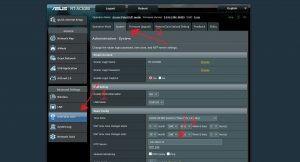
17. Configure the NTP server. Navigate to the “administration” tab and then “system”
– Adjust your NTP server to 192.168.0.12. Type this IP in if the setting is blank.
18. If you do not want this router to advertise its IP’s as the network DNS server, make sure to disable dnsmasq. To do this:
– Select “operation mode” to the left of system.
– Change your operation mode from “wireless router mode” to “Access point”.
IMPORTANT. You will have to re enter the IP of your router again to avoid reverting it to the default IP.
19. ALL done! You have finished your router setup! You now have the fastest internet on your street.
How to set up your RT-AC5300 ASUS router by Francesco Kacperski